Not the leisurely activity you may enjoy on a cool Saturday morning, phishing – and its close cousin, spear phishing – are two of the most targeted cybersecurity attacks individuals and organizations may encounter.
Phishing is one of the most popular social engineering attack types. Phishing scams are email, text message (Smishing), and voice calls/voice messages (Vishing) campaigns aimed at creating a sense of urgency, curiosity, or fear in victims, which prods them to reveal sensitive information, click on links to malicious websites, or open attachments that contain malware.
Meanwhile, spear phishing is a more targeted phishing scam where the bad actors choose specific individuals or businesses. They tailor their messages based on characteristics, job positions, and contacts belonging to their victims to make their attacks less noticeable. Spear Phishing is a more sophisticated form of phishing attack that can take weeks and months to pull off. It’s much harder to detect and has a better success rate if done skillfully.
These cybersecurity attacks can have a negative impact on organizations, such as business and operational disruption, data exposure, reputational damage to the organization, and serious financial implications.
As part of Cybersecurity Awareness Month, we’d like to help you learn about these two dangerous threats and prevent you from being a cyber criminal’s catch of the day.
Phishing: How Bad is It?
According to the National Cybersecurity Alliance’s (NCA) Oh Behave: The Annual Cybersecurity Attitudes and Behaviors Report 2023, phishing accounted for almost half (47%) of the 2,047 cybersecurity attacks that led to losing money or data.
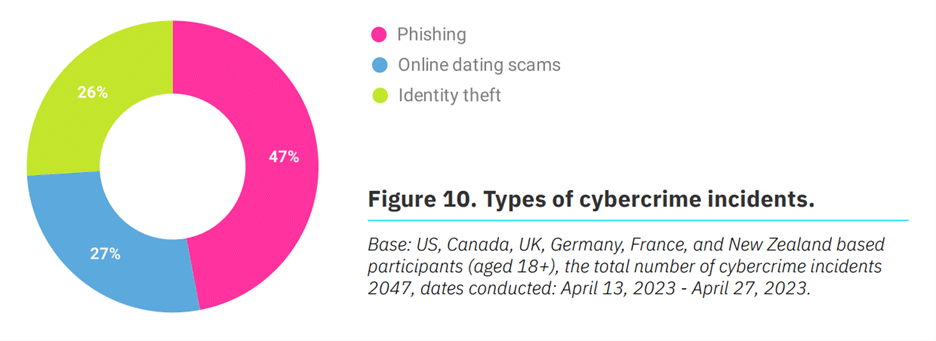
Image Source: Oh Behave: The Annual Cybersecurity Attitudes and Behaviors Report 2023
Recognizing Phishing Messages
This high incident rate of phishing can be attributed to the volume of people who still do not have enough knowledge to recognize phishing. While more than two-thirds are either “confident” (41%) or “very confident” (25%) in their ability to see through phishing, the remaining third is “not at all confident” (6%), “unconfident” (7%) or “neither confident nor unconfident” (21%).
The cybersecurity report also found that 44% “always” check messages for signs of phishing.
How do people recognize a possible phishing attack? More than half (54%) check the sender’s email address and close to a third (29%) look at content and spelling errors. Only 14% verify email links by hovering on the URLs. To add an extra layer of protection, using a DKIM checker and implementing DMARC rules can help prevent phishing by ensuring that only legitimate emails are delivered and blocking fraudulent ones from reaching inboxes.
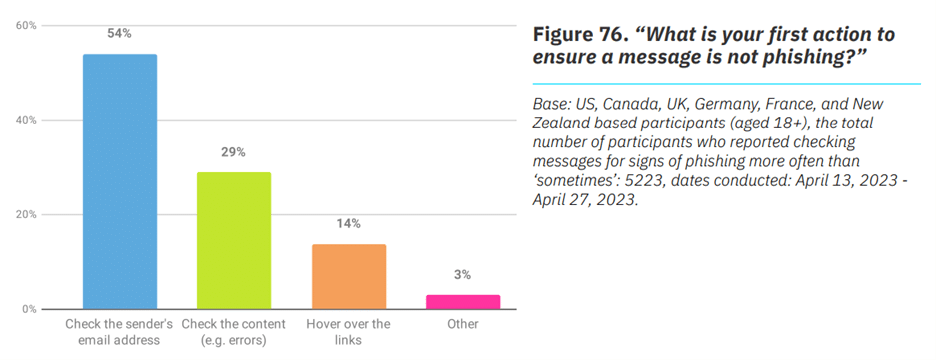
Image Source: Oh Behave: The Annual Cybersecurity Attitudes and Behaviors Report 2023
Reporting Phishing Scams
When encountering phishing scams, about one-third (33%) “never” or “rarely” report them using the “spam” and “report phishing” buttons that are usually integrated into email and social media tools. And despite the convenience of having these report buttons, a combined 8% don’t know how to use them or can’t find them at all.
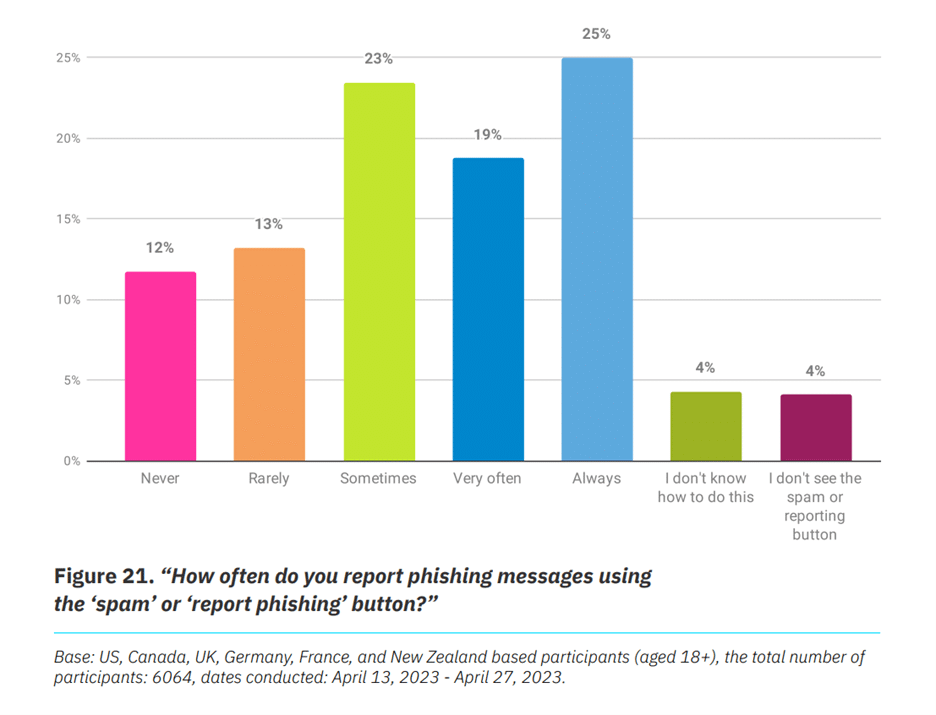
Image Source: Oh Behave: The Annual Cybersecurity Attitudes and Behaviors Report 2023
Despite this, reporting still improved significantly compared to 2022. Among those who fell victim to phishing, 86% reported the incident in 2023, leaving only 14% unreported instances. In 2022, a considerable 31% of phishing incidents went unreported.
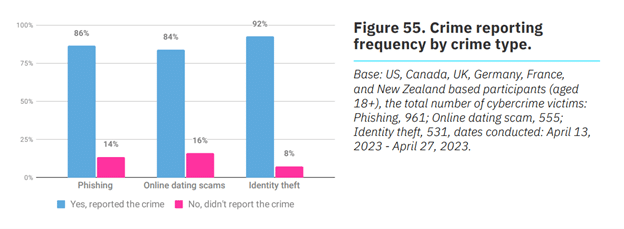
Image Source: Oh Behave: The Annual Cybersecurity Attitudes and Behaviors Report 2023
For victims who did not report the cybersecurity attack, their top reasons were the amount of money or data lost was negligible or unimportant (19%), and they felt that reporting would not translate to a course of action from the authorities (18%).
11 Cybersecurity Tips to Avoid Falling Victim to Phishing
How can you prevent being on the wrong end of a social engineering attack? Here are some of the best cybersecurity risk management practices you can implement:
- Conduct cybersecurity awareness training for employees to help them identify phishing attacks, e.g., avoiding clicking on malicious links and attachments. Of people who have access to cybersecurity training, 68% are able to learn about identifying phishing messages, and 50% become better at recognizing and reporting phishing messages.
- Conduct random mock phishing exercises.
- Implement Multi-Factor Authentication (MFA) on your organization’s critical applications and systems. Almost a third (30%) still haven’t heard of MFA, and 11% of people who have heard of it don’t know how to use it. Informing employees on how to use MFA is vital.
- Keep all systems and applications current with the latest security patches and updates.
- Deploy a web filter to block malicious websites.
- Encrypt all company-sensitive data.
- Remote access to company data should be executed through the company’s Virtual Private Network (VPN).
- Conduct regular user access reviews (UARs) on all critical systems and applications.
- Encourage employees to have a complex password/passphrase, which should not be used for other accounts, and password/passphrase should be treated as the keys to the kingdom.
- Regularly analyze and evaluate your internal security processes to make sure your applications and systems are not easily exploitable.
- Have a dedicated contact for employees to report any suspicious activity or activities. At AvePoint, that is our PSR team. We stand ready to ensure we live up to our mission to place safety at the hearts of our customers and people every day.
How AvePoint Addresses Phishing for People & Customers
At AvePoint, we have a simple yet profound mission: to place safety at the heart of our customers and our people.
For our people, we conduct regular cybersecurity awareness training, internal articles, and social media posts with new tips following the evolving sophistication of social engineering and routinely hold mock phishing exercises.
When it comes to our systems and customers, we ensure that our cybersecurity awareness training complies with the gold standards of privacy and security accreditations, including ISO 27001, GDPR, and CCPA. We also stay on top of the latest cybersecurity trends – like the rise in ransomware attacks, vendor risk, remote working, mobile cybersecurity, cloud security threats, and social media engineering attacks – and assess how they impact our systems.
To learn more about how we embed trust as the core principle into our systems and people, visit the AvePoint Trust Center.