Want more information on Office 365 security and compliance? Read our Mitigating Collaboration Risk eBook.
Read the other post in our Securing Collaboration series below:
- How to Get ISO 27001-Ready
- Oversharing Challenges in Microsoft 365
- Sensitive Info Identifiers in Office 365
- How to Find Sensitive Information in Office 365
- 5 Risk Management Challenges in Office 365
- How to Build a Strong Permissions Management Strategy
- Office 365 Governance in an Always Online World
- When to Upgrade From E3 to E5 for Stronger Microsoft 365 Data Protection
Office 365 Security & Compliance Center Tips
The Security and Compliance Center in Microsoft 365 has tons of great tools to find sensitive information and help you make your environment more secure. There’s a LOT of features and admin tools in the Security and Compliance interface though, and it can be confusing to know where to begin!
To help you with enforcing security in Microsoft 365, I’ve compiled some tips and tricks below to help simplify securing you collaboration information.
Organization-Wide Data Retention
Lots of organizations have internal SLAs or regulatory requirements to hang on to certain types of data for a specific period of time. Once this time is up, it’s important to remove such records to reduce the liability that comes from exposure to certain information.
Retention labels and policies allow organizations some level of control for managing the information lifecycle, as well as report on the types of information within their environment.
Now, for organizations that are looking for a little more control, there are also records management features within the Security and Compliance Center.
Retention labels and policies however, are a fast and easy way to apply retention and deletion policies across Office 365. They are also a great place to get started with data governance and security for any organization.
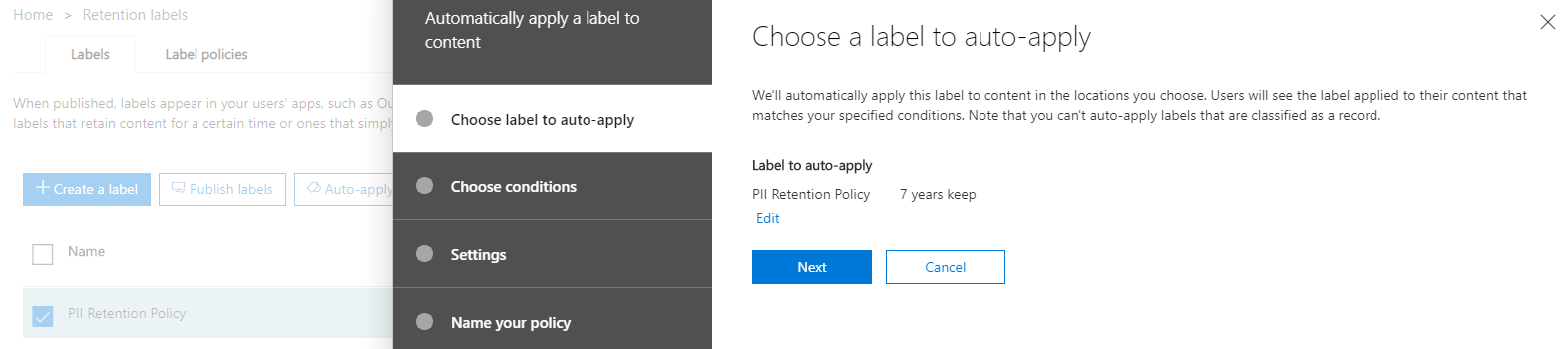
Using Retention Labels for Other Policies
Retention labels can be used for far more than retention. They are primarily used to tag information in Microsoft 365 for the enforcement of content lifecycle management, but did you know that you can setup other policies in the Security and Compliance Center to reference your retention labels and policies?
Some organizations don’t have regulatory requirements but are concerned about Personal Identifying Information (PII) and sensitive information in their environment. In these cases, applying broad Retention Label policies that can be reused for (data loss prevention) DLP and sensitivity labels is one strategy to give you lots of visibility into your sensitive data without having to setup a bunch of unique policies in Microsoft 365.
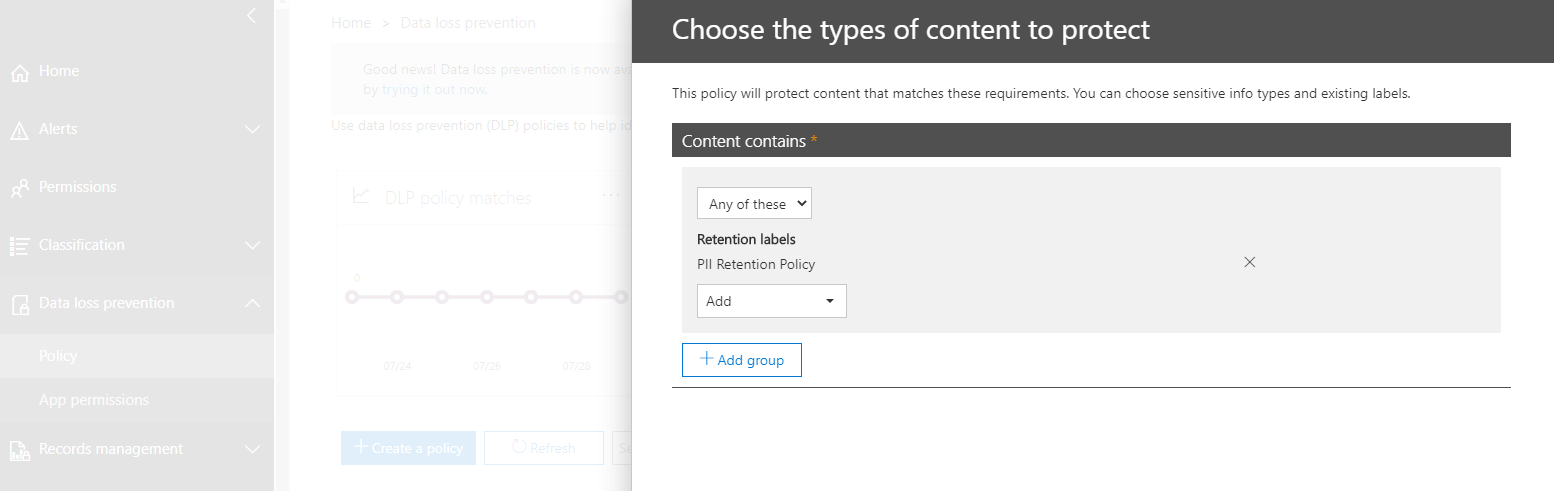
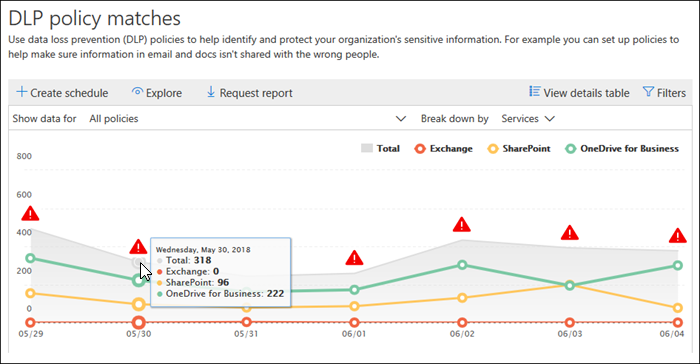
DLP Policies
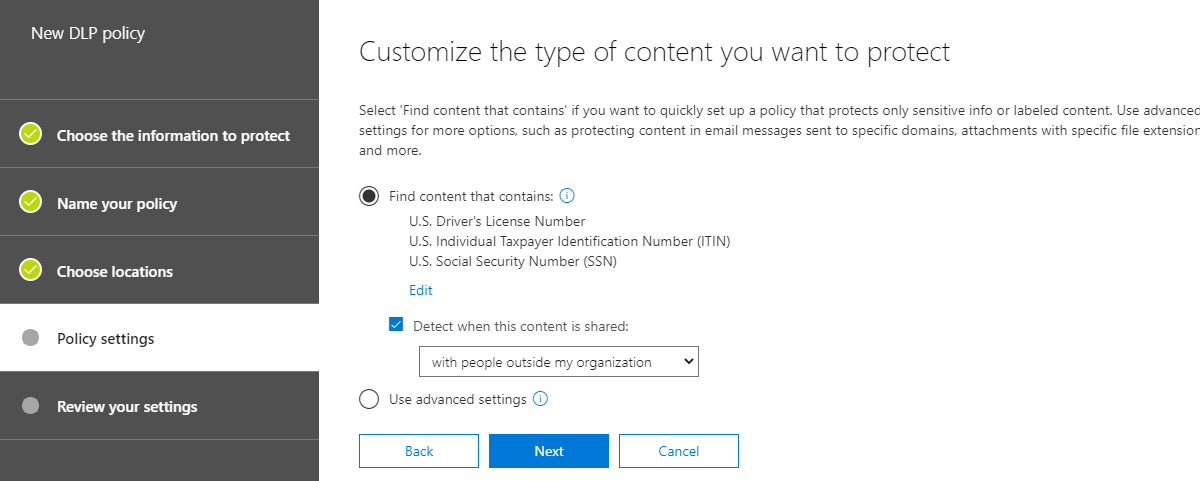
DLP policies are a great way to quickly understand which documents in Microsoft 365 have sensitive information. You can even use the reporting to quickly understand which ones have many instances of content that matches sensitive information types.
Sensitivity Labels
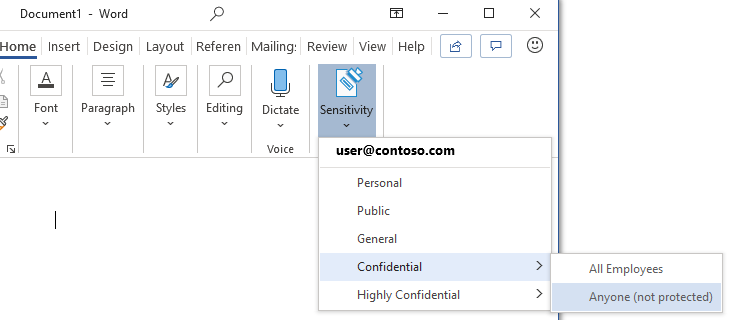
Sensitivity labels are a great way to add an additional layer of security and control to your Microsoft 365 content. When users apply sensitivity labels to the confidential documents they create, your policies are applied to enforce the rules you set up associated with those labels.
With an E5 license, those labels can even be automatically applied! If you want, you can base your sensitivity labels around your retention label policies, or you can come up with your own policies for each sensitivity label for more control.
Custom Sensitive Information Types
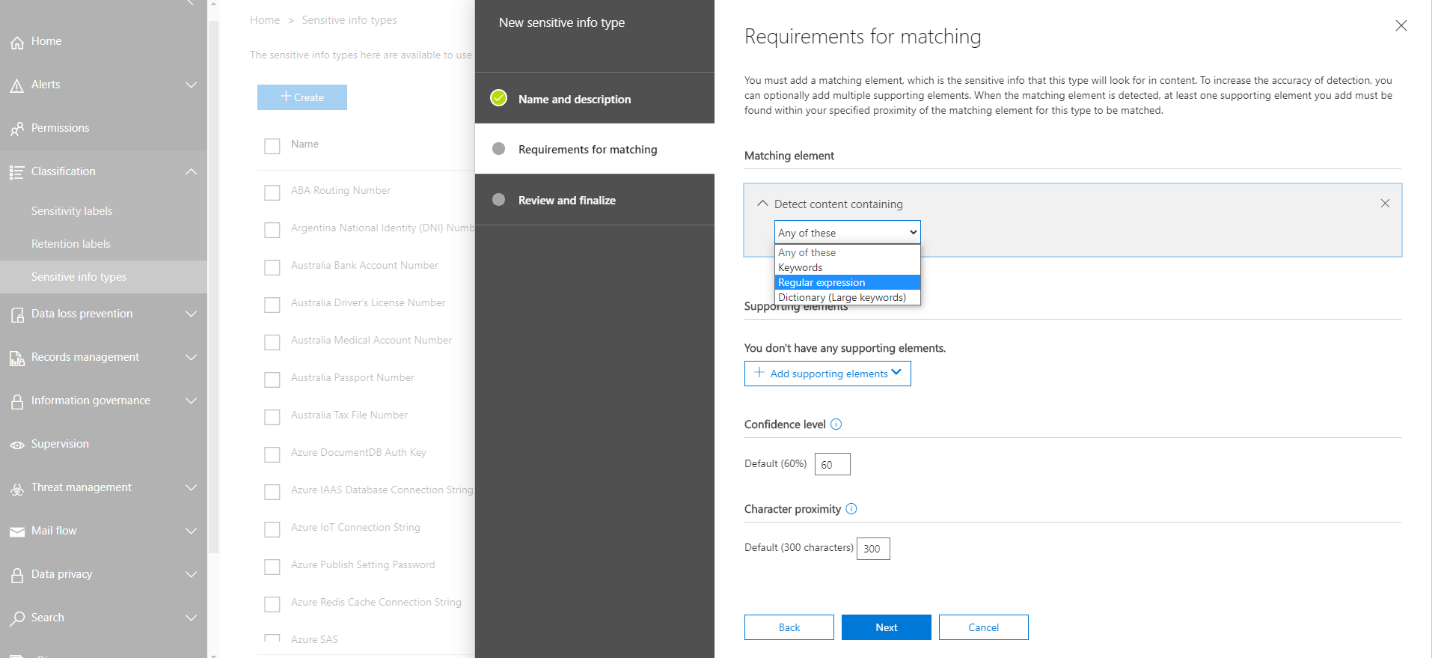
Microsoft 365 has had many sensitive information types for a long time but did you know that it’s now possible to create sensitive information types in Microsoft 365?
You can actually create a new sensitive information type from scratch using keywords, a regular expression of your own, or from choosing from dictionary keywords. You can use a custom sensitive information type with any of the policies that use them.
Balancing Policies & Managing Access in Microsoft 365
These are just some quick tips and tricks to get started managing information in Microsoft 365! It’s important to understand though, that while there are many tools to attempt to mitigate sensitive information and exposure to certain kinds of documents, there’s not really an interface that gives a comprehensive view of who has access to certain kinds of information, nor a way to prioritize sensitive information based on exposure or location.
In addition, it can be very difficult to apply and keep track of so many policies in ways that scale with your organization’s growth while still meeting the needs of your users.
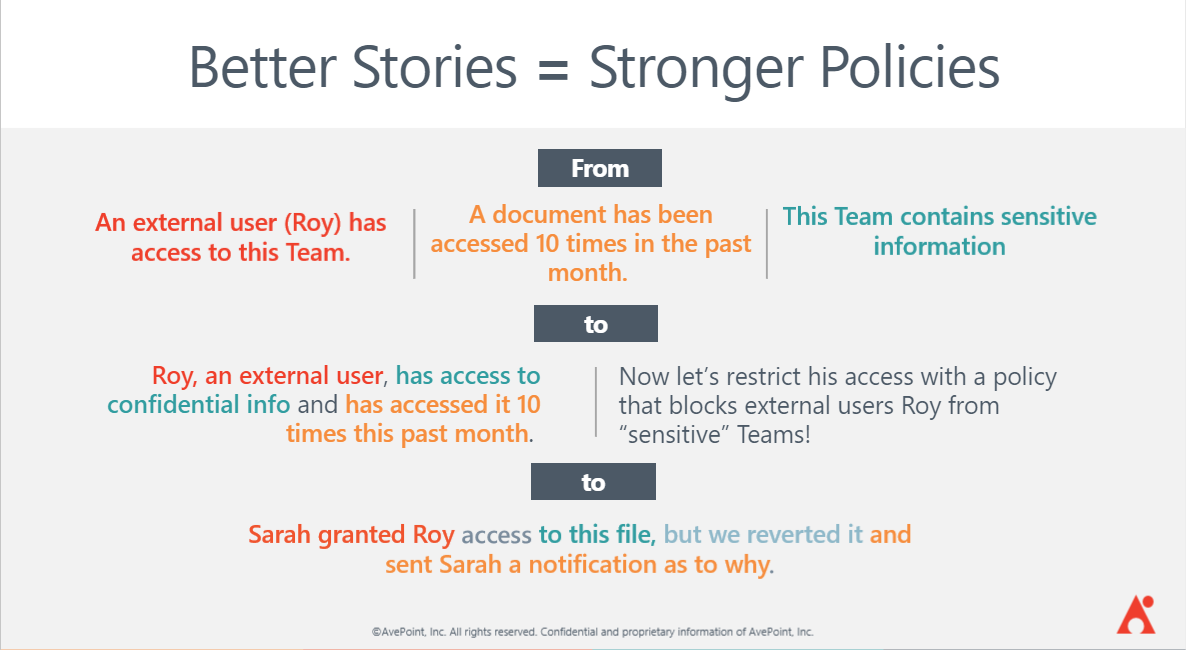
AvePoint’s new Policies and Insights Solution does all this heavy lifting for you! Policies and Insights (or PI) gives you the tools you need to understand who has access to what in easy ways, while also making it quick and easy to understand where your sensitive information exists. Most importantly, PI gives you the tools to prioritize sensitive information based on how many people have access to it, and who those people are.
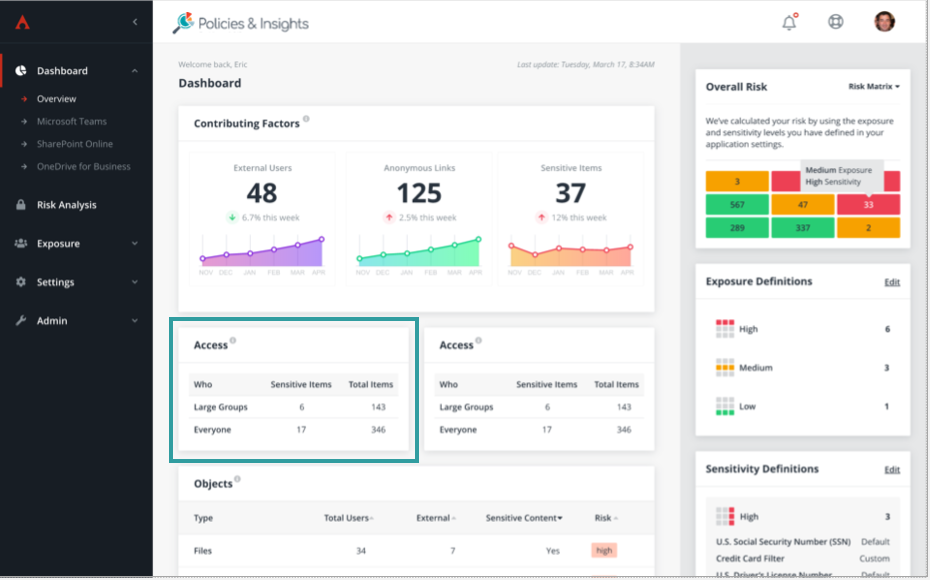
PI is also one of the only solutions that doesn’t require you to constantly look at reports and make manual changes across your environment- PI can automatically enforce security and other settings, reverting out of policy changes or notifying the necessary parties when they occur.
If security and risk mitigation are becoming a higher priority for your organization, be sure to set up a time to chat with us and how we can help. And for a bit more on Policies and Insights, check out the video below:




