AI agents are changing how work gets done. They’re helping teams summarize, automate, and create at a pace that was impossible even a year ago. The excitement is real — but so is the complexity.
As new agents come online across multi-cloud environments, organizations are asking the same questions: Who created them? What information are they accessing? Are they still being used? Is this safe? Am I mitigating risk? Is this driving ROI and business value?
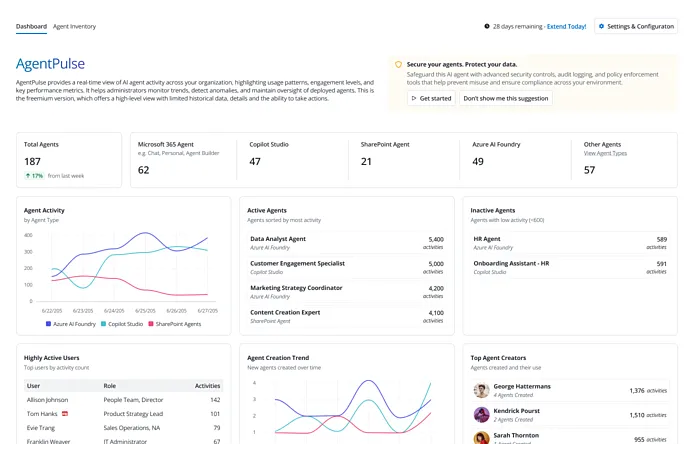
AgentPulse Command Center, the latest addition to the AvePoint Confidence Platform, serves as the front door to AI agent control. As a centralized command center, it gives leaders a complete picture of the agents operating across their environment so they can take steps to manage them responsibly.
Seeing What Was Once Invisible
Many organizations already have thousands of agents working in the background. Some are built in Copilot Studio, others in Azure AI foundry, or third-party applications. Each connects to data, interacts with systems, and contributes to outcomes; yet, many remain invisible to IT and security teams.
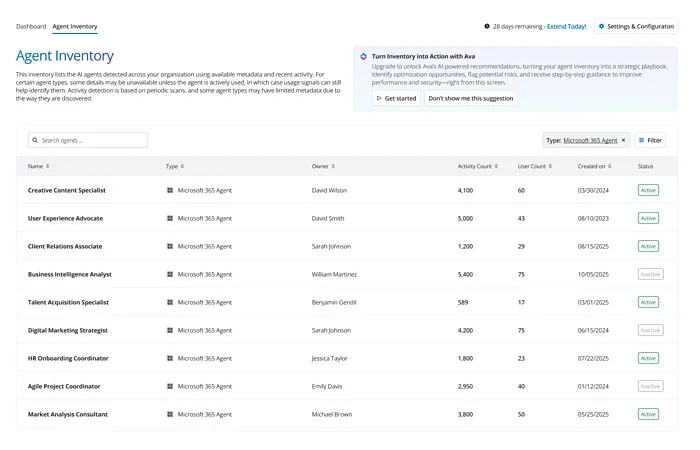
AgentPulse brings the full agent ecosystem into view with automated discovery that identifies and maps every agent across your digital landscape. Supported environments include:
- Microsoft 365, including Copilot Studio, personal agents, and chat agents
- SharePoint
- Azure AI Foundry
- Independent Software Vendor (ISV) Store
Once discovered, each agent is enriched with key metadata, including who created it, when it was last used, what data it interacts with, and the business context behind its purpose. That visibility allows teams to make informed decisions about which agents are valuable, which pose risk, and which should be retired.
From Oversight to Ownership
Governance has always been at the heart of responsible innovation. AgentPulse extends that foundation into the era of agentic AI.
With AgentPulse, organizations can manage AI agents with the same discipline they apply to users, data, and workspaces, without adding manual overhead. Through automated lifecycle management, every agent stays aligned with internal policy and is securely maintained over time.
Key capabilities include:
- Agent lifecycle automation. Manage creation, ownership, renewal, and archival in one place.
- Contextual governance. Track each agent’s purpose, data sources, and approval status.
- Policy alignment. Enforce reviews, renewals, and deactivations on schedule.
- Cost awareness. Identify inactive or redundant agents driving unnecessary spend.
This structure reduces compliance risk while spraring IT teams from performing repetitive oversight. As organizations mature their AI use, it turns experimentation into a sustainable, scalable practice.
Context Builds Confidence
Raw data alone isn’t enough. What makes AgentPulse powerful is the context it provides, along with the ability to act on those insights through the Confidence Platform. Beyond simply counting or categorizing agents, it connects technical information – like access and activity – with business insights about purpose and performance.
Because this visibility is drawn directly from your environment, rather than self-reported or siloed views, it provides leaders with a clearer and more reliable picture of what’s happening across their tenant. That context helps teams understand which agents truly drive value and which introduce unnecessary risk. When governance is rooted in understanding, it prevents exposure and enables smarter, more strategic growth.
Meeting the Moment for AI Accountability
As discovered in this year’s State of AI report, 75% of organizations using AI experienced a data breach in the past year. Gartner also predicts that 40% of agentic AI projects could be abandoned by 2027 due to inadequate risk controls.
These numbers don’t signal a lack of innovation as much as they highlight the need for stronger oversight. AgentPulse extends AvePoint’s proven governance model to AI agents, giving organizations the same foundation of trust and accountability they already rely on for users and data.
With AgentPulse, organizations can:
- See every AI agent across platforms and environments.
- Identify security and compliance risks before they create exposure.
- Reduce manual effort through automated policy enforcement.
- Improve ROI by aligning AI activity with business objectives.
Because innovation is only sustainable when it’s secure — and security is only achievable when organizations have full visibility and governance. AgentPulse brings both to the forefront, transforming AI from a potential liability into a confident advantage.
Your Command Center for Responsible AI
AI has already changed the way we work. The next step is transforming how we stay in control of it.
AgentPulse gives organizations the clarity and context to make that possible. It turns visibility into action — helping leaders understand not just what’s happening across their environment, but how to respond.
With that insight, teams can:
- Empower creators to innovate responsibly with clear guardrails.
- Strengthen collaboration between IT, security, and business units.
- Anticipate risk instead of reacting to it.
- Scale new initiatives with confidence, not guesswork.
The goal isn’t to slow innovation; it’s to make it sustainable. When organizations know which agents exist, what they touch, and why they matter, they can make AI a trusted part of how work gets done.
Take control of your AI ecosystem. Discover how to make AI accountability your competitive edge.

