Editor’s note: This is the second post in a series around identity management in Azure Active Directory. Check out the first post here and the others below!
- 9 Things to Consider when Preparing for The SaaS Future
- Why IT Admins Can’t Think in a Siloed Fashion Anymore
- 5 Tips to Understanding License Models in the SaaS World
- Why Role-Based Access is Key for Strong Data Security
Secure identity management on-prem or in the cloud
Most of us only worry about our ID when we need to prove to others who we are. In the online world, we actually do this on a regular basis. This process affects you more directly than you might think. Whether you login to Facebook, Gmail, or Microsoft Office, you’re proving your identity to a system and that you are who you say you are.
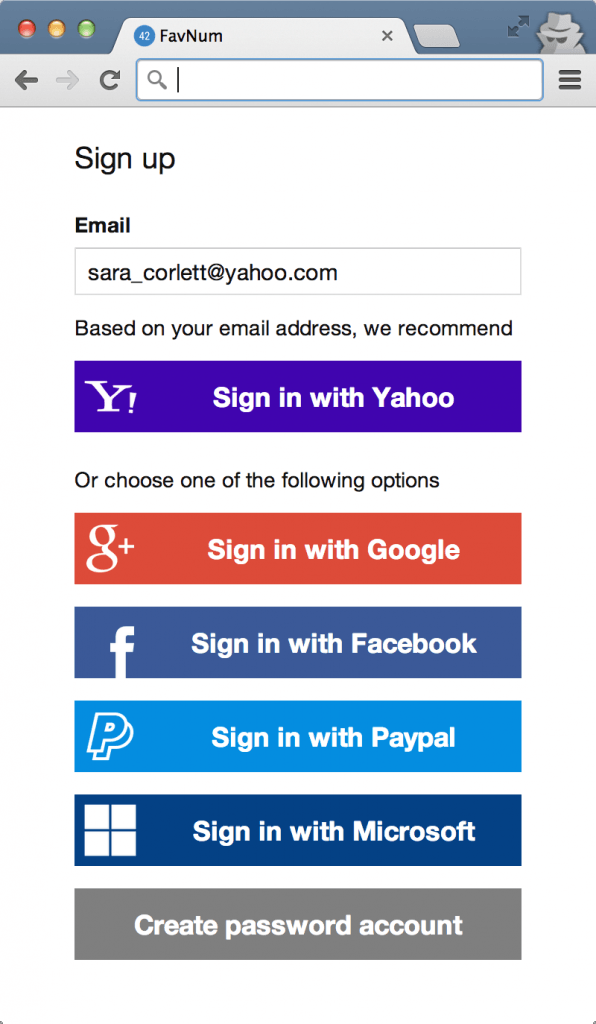
Most systems rely simply on an active username and valid password. Many more are now requiring Two-Factor Authentication (2FA) as a form of access to a system. Many more secure systems include multi-factor elements, such as identity, PIN, activity session timeout, and access-only from certified devices.
Each one of these processes builds walls and restricted paths around accessing a system. From my experience, there’s a balance to be had here between secure access and level of effort to log into systems. Most businesses seem to be on the reactive side of secure identity management in this regard, and we need to look further into how different teams play into this system.
Processes to ensure secure Active Directory identity management
1) When you are employed by a company, your identity as an employee and an agent of a company carries specific rules and requirements for both you and that organization. Companies compensate you with money for your time and efforts to create value, and as such, they often provide IT services, such as laptop, email, and mobile devices to get you productive from the get-go.
2) In order to provide licensed products for you to work, IT services needs to create and originate an identity for you. This can come from HR, such as an email, employee ID, or a request to create a new account.
3) Depending on what your position is inside the organization, your role will vary. Most Identity manager systems allow the creation of buckets to put users in. Administrative staff versus sales employees, or management, are all different buckets with specific roles and privileges.
4) Where things often break down: Communication between teams is often just not there until after the fact. Users come and go from companies all the time. Increasingly, the gig economy is becoming a part of the regular workforce, so the question is whether or not companies will simply allow access to your identity and when jobs are complete you get locked out. This has many ramifications for how business work and share content.
Some best practices to ensure secure Active Directory identity management
5) Check between HR and IT Admin services on a regular interval for the active and inactive users in the system. Simple secure lists can help enable this.
6) Task it out to complete it.
7) If more immediate needs exist, have an email system in place, workflow, forms, etc.
8) Establish SLAs between different units in the organization.
9) Check, prove, review.
10) How this changes in cloud services and SaaS- when users come and go from a multi-tenant system, part of the user agreement mostly surrounds active users. If a user leaves, content may be slated for deletion after a period of time.
This affects access to content that used to go stale on-prem. This should be a concern if content a user worked on is subject to regulatory or legal procedures. Something you should be aware of in systems such as Office 365 or Gmail.
11) Process to archive, backup, and ultimately delete content from inactive users
a. We do not live in a file share- nor should anyone anymore!
b. Help to mitigate potential legal costs from eDiscovery by deleting ROT data or data that has reached its expiration date.
Like what you read? Be sure to subscribe to our blog to stay in the fold for all things Office 365, SharePoint and more!

