Worried about leaks in Teams and other Office 365 apps? Check out our free webinar “Preventing Data Leaks in Microsoft Teams (and Other Collaboration Systems)” for must-know tips.
Read the other post in our Securing Collaboration series below:
- How to Get ISO 27001-Ready
- Oversharing Challenges in Microsoft 365
- How to Find Sensitive Content in Office 365
- 5 Risk Management Challenges in Office 365
- Top 5 Microsoft 365 Security and Compliance Center Features and Tricks
- How to Build a Strong Permissions Management Strategy
- Office 365 Governance in an Always Online World
- When to Upgrade From E3 to E5 for Stronger Microsoft 365 Data Protection
We all know that Office 365 has all sorts of security features to help us mitigate risk caused by exposure to sensitive information in Office 365. This doesn’t just include controlling access to files via permissions either.
With an Enterprise license in Microsoft 365, robust features like applying retention and sensitivity labels and reporting on sensitive information across your Office 365 environment enable you to understand what sensitive information exists. It’s also possible to report on and protect files with Data Loss Prevention (DLP) policies without having to apply a label to documents that meet your criteria.

What is the driver behind all these capabilities? How does Microsoft 365 know what to protect and what has sensitive information in it? Well, every Microsoft 365 tenant with an enterprise license also comes with a massive set of sensitive information definitions that it uses to root out content that may be subject to regulation or cause risk in your environment.
Sensitive Information Identifiers in Microsoft 365
Sensitive information identifiers are coded entities that Microsoft 365 uses to discover important content within documents.
As Microsoft 365 scans documents for search and other purposes, it indexes that content. If you setup a DLP policy or retention label based on the Sensitive Information Types, files with content meeting the sensitive information type definitions will be indexed for reporting and taking action on.
What Information Types Are There?
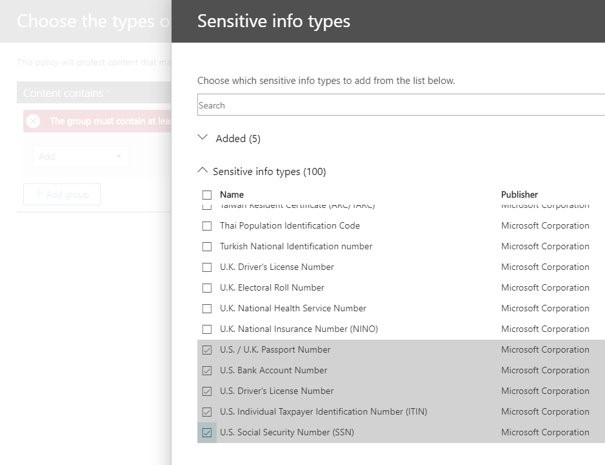
Microsoft has over 100 definitions for sensitive information. Many of them are geared towards finding personal identifying information standards for different countries and regions. You can also create your own custom sensitive information type by combining the existing definitions or adding keywords or regular expressions. This can help organizations meet GDPR and other regulatory requirements more broadly. There are also other legal and healthcare definition types to help ensure that healthcare or medical information in Microsoft 365 is kept secure.
Once Sensitive Information is Found…
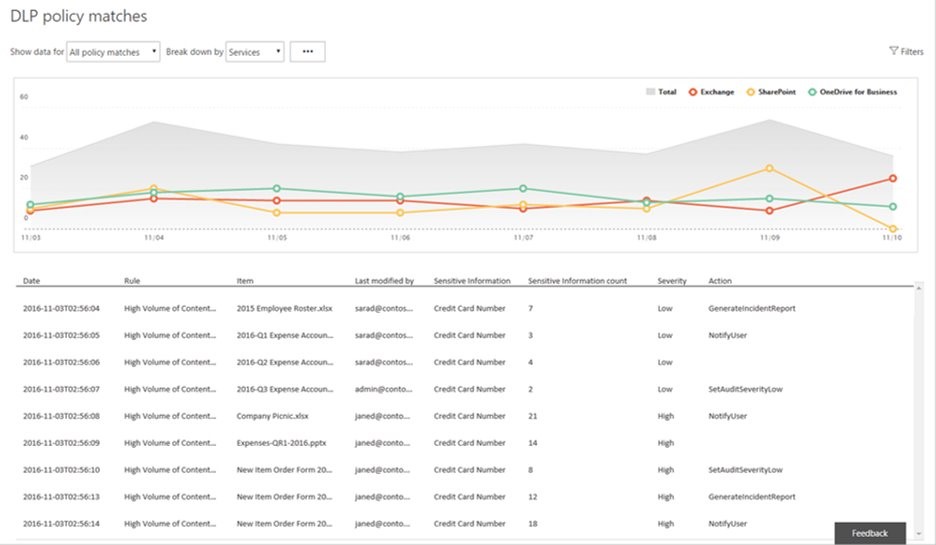
Organizations can report on DLP policy results as found by Microsoft 365 for a better understanding of what documents contain sensitive information and where these documents are located. Policies can also help ensure that no documents with sensitive information found by the DLP engine can be shared externally.
There are tools to assist in reducing false positives and to tune and adjust your DLP and sensitive information type settings for best practices. It’s also possible to apply these policies to only a specific set of locations or applications in Microsoft 365.
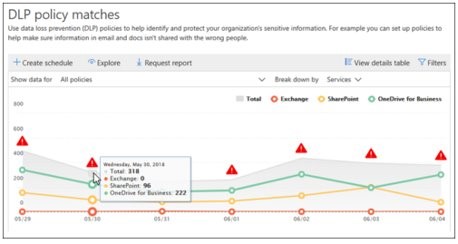
The DLP reports will highlight documents with multiple hits for definition types as being more sensitive than documents that only have one hit. The more sensitive information in one document, the more sensitive the document is considered to be.
Microsoft has loads of documentation where you can learn more about their DLP policies and labels that can help you secure your environment. Additionally, we’re also going to be continuing our AvePoint series on security and compliance features, what’s available, why it’s important, and more strategies to secure your sensitive information in Office 365.
Aggregate Reports and Automate Permissions Corrections
AvePoint’s new Policies and Insights solution automates how policies can be applied to Microsoft 365 so you don’t have to. Policies and Insights (or PI) aggregates security reports with sensitivity and audit activity to automatically prioritize your sensitive content exposure before giving you the tools to mitigate it.
Using the existing sensitive information identifiers in Microsoft 365, it’s a quick and easy process for our SaaS application to not only root out sensitive content but dive into all the users who could potentially access it. We then prioritize the urgency of content-based risk by contrasting the sensitivity of the content, its internal and external exposure, and the audit activity to give a more complete aggregated picture of what documents are truly creating risk in Microsoft 365.
Then, we give you the tools to automate corrections to security and settings to ensure you can reduce the exposure over time!
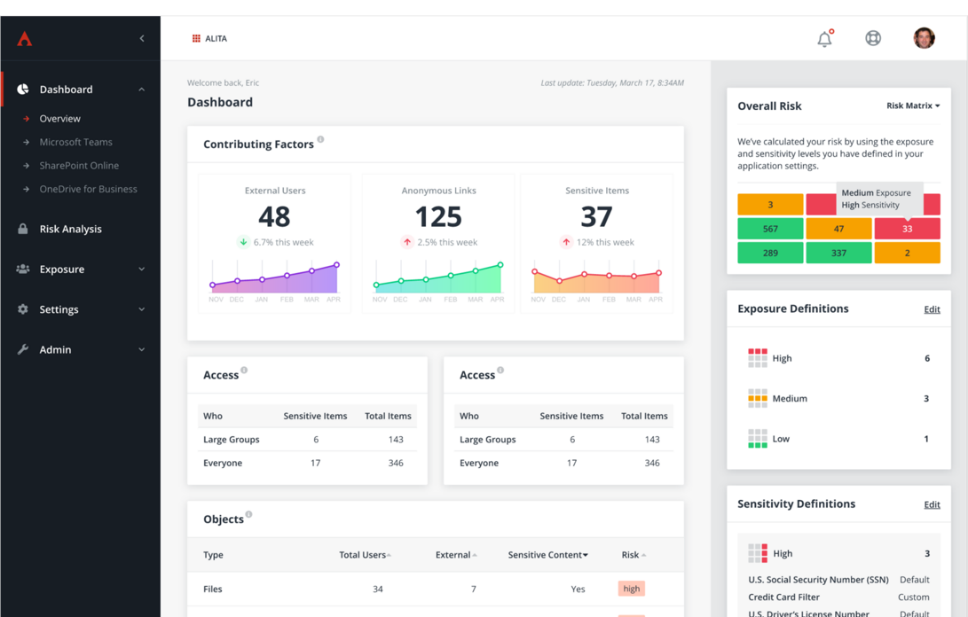
PI enables organizations to reduce their operational burden of managing policies and security settings in Microsoft 365 and automates corrections to permissions, classifications, and settings. Prevent configuration drift and enforce security without hindering organizational collaboration so you and your users can rest easy!
For a bit more on Policies and Insights, check out the video below:

![[WGR] PI Blog Series Headers_4 office 365](https://www.avepoint.com/blog/wp-content/uploads/2020/07/WGR-PI-Blog-Series-Headers_4-696x299.png)