It’s no surprise that organisations continue to experience data sprawl, largely driven by digital transformation efforts and collaboration technologies. 78 percent of the respondents in the Association for Intelligent Information Management (AIIM) 2023 State of the Intelligent Information Management Industry report stated that technology usage is driving the vast volume, velocity, and variety of information that is flooding their organizations. In fact, businesses now find themselves facing significantly higher data storage costs—and even costly overage fees. One report found that more than one-third of companies have cloud service budget overruns of up to 40 percent.
With all that content in play, information management is projected to become more important, however one-third of AIIM’s survey respondents rated their organizations below average in core information management areas such as managing information through its lifecycle and applying governance and compliance.
Unfortunately, it’s not just storage costs that are on the rise – so is your risk. Holding on to too much information can increase your chance of facing regulatory, operational, or security-related risks. While storage budgets will likely never return to pre-pandemic levels, you can mitigate your data volume and manage your risks by proactively applying the aforementioned information lifecycle principles.
As an AIIM Board Member, I’ve had the good fortune to speak with information management colleagues from organisations large and small, public and private. While their resources and experiences vary, of course, a consistent theme has emerged—a commitment to delivering value through the application of robust information lifecycle practices.
At this year’s AIIM Conference in New Orleans, we were proud to host a group of students from local Louisiana universities. Many of these students had a broader interest in technology and were surprised to find just how much information managers are harnessing the power of technology to accomplish their operational imperatives and improve the user experience—and that was before the conversation turned to AI and emerging technologies! Just imagine what the future holds. I know I am.

[Please enjoy this excerpt from the 2023 State of the Intelligent Information Management report]
As we look back at the state of the industry across the past ten years, it is easy to use hindsight to attempt to address areas of contention or where a lack of progress has been made. However, our research also asked respondents to look to the future in several areas.
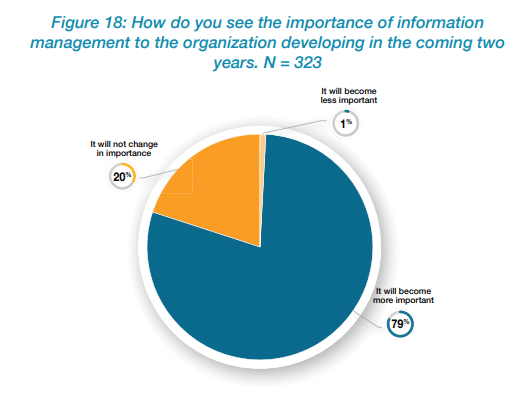
The Importance of Information Management
Asking an audience that works in information management whether that area will become more or less important in the next two years might seem like a pointless exercise. However, you might expect that asking the question to both an AIIM audience and a non-AIIM audience would yield different outcomes. In fact, the two audiences provided very similar results. Overall, 79% of the combined audience sees information management becoming more important over the next two years — constructed from 84% of the AIIM Audience and 72% of the non-AIIM audience. Only 1 % of the combined audience feels that information management will become less important. The strength of awareness of the importance of IM across the entire business audience is encouraging. Information management has struggled to gain visibility with executives, being seen as only a necessary cost center. However, we now live in a world where remote working and digital information are the default — making information management a term and discipline everyone needs to consider. This change provides a vast opportunity for IM vendors, practitioners, and advocates to discuss how they can help with the whole business.
Skills Requirements
Continuing the forward-looking aspect, we asked respondents which skills they believe they need to achieve their goals at the organizational, departmental, and personal levels. Not surprisingly, information governance (IG) and information management (IM) both ranked highly — IG was slightly higher for the organization and department, whereas IM was higher for the department and individual.
Leadership skills were identified by around 1 in 5 (22%) respondents as a critical need at an organizational level – mirroring the earlier findings that a lack of leadership is hindering ongoing digital transformation.
Equally of interest is the mismatch of the skills individuals desire compared to the needs of the organization and department. For example, data analytics, project management, communication skills, and development/coding are desirable for individuals but appear to carry less weight to the business. For leaders within IM groups, marrying the ongoing career aspirations of their teams with the needs of the business will be critical to maintaining a happy and effective workforce.
The Mood of the Industry
To gauge feeling around a series of more subjective topics relating to information management, we asked our audience to indicate their level of agreement against specific statements.
Return to the Office
As we move forward into 2023, we find a split view concerning a return to the office — 41% believe they will return to a largely office-based mode of working, while 38% disagree. Fortune Magazine reported that office occupancy rose to over 50.4% in late January 2023 but dropped then to 48.6% by late February 2023. For many working in information management, remote working does not pose technical issues — they have been digitally enabled for years. However, there are documented cultural and sociological benefits of in-office work. Perhaps the answer is not one or the other — remote vs. Office — but a balanced, hybrid workplace approach.
Removal of Paper Invoices
Paper usage within organizations has been decreasing for years but still exists — at least within the accounting department. Only 49% of our respondents think they will have eradicated paper invoices by 2025, with a quarter (25%) actively disagreeing. Invoice processing is a focus for information management, with significant emphasis from almost every vendor in the space. There is an opportunity for organizations to explore why paper invoicing is still needed, the cost of continuing, and the roadblocks preventing digitalization.
Technology Usage Driving Info Chaos – but also winning the war
Technology is proving to be a double-edged sword for many. A huge majority (78%) feel that technology usage is driving the vast volume, velocity, and variety of information that is flooding their organizations. However, just over half (55%) also believe technology is winning the war against information chaos. Organizations use more information systems than ever (see section above). Logically, this influx of systems is driving more volume, velocity, and variety into the IM part of the business — but is it also helping control the overall information chaos? Careful thought should be applied when introducing a new system, technology, or approach to ensure that it meets business requirements and does not add to the information chaos challenge.
To read more, download your complimentary copy of the 2023 State of the Intelligent Information Management Industry report, presented by AvePoint in partnership with AIIM.
How much data do you create and store each year? Use our data storage calculator here.