The proliferation of generative artificial intelligence (AI) into the business landscape continues to expand: Nearly half of US executives are already on board with the idea of generative AI, with 44% planning to increase their use of AI at their organization in the next year. It’s clear the future of work is AI-powered.
As we move from the novelty of simple tasks transformed with generative AI to solving real business problems, Microsoft 365 Copilot will be generally available on November 1. This groundbreaking AI-powered assistant can help you with a range of tasks, from creating and editing documents to preparing demonstrations, to streamline repetitive tasks and increase productivity.
As with any new technology, proper preparation is necessary to make sure you maximize the benefits of AI. Without it, the rewards of AI can be overshadowed by the potential pitfalls, particularly when it comes to data security. In this blog post, we’ll explore how to ensure your environment is ready for AI and provide practical steps you can take to get there.
Can Microsoft 365 Copilot Put Your Sensitive Data at Risk?
Deploying Microsoft 365 Copilot can be an exciting step for organizations looking to leverage AI to take their organization to the next level. However, this excitement can quickly turn to concern when you truly understand just how much data Microsoft 365 Copilot can access. A Gartner study explains that Copilot supports easy, natural-language access to unprotected content, which exposes the risk of sensitive data exposure.
For instance, an AvePoint partner faced this scenario when deploying Microsoft 365 Copilot. Once launched, they realized it was accessing more data than intended. Their CISO shut down the project until they could figure out how to lock down this information.
While this in itself isn’t a fault of Microsoft 365 Copilot – Microsoft designed it to protect your privacy and leverage compliance and security capabilities that always put the user and organization in control – your use of it will only be as good as your organization’s controls because you are in the driver’s seat of your data.
Your Microsoft 365 Copilot deployment will only be as good as your organization’s controls because you are in the driver’s seat of your data.
Consider this scenario: you think your compensation documents are safely tucked away in a SharePoint site intended for your Human Resources Team. Yet if this site and its files do not have proper access controls in place, anyone in the organization using Microsoft 365 Copilot can access it. All one of your employees needs to do is ask, “What’s my salary?” and Microsoft 365 Copilot may share not only that employee’s salary but also a whole document detailing the compensation of the whole team – or even the entire organization.
In our partner’s situation, Microsoft 365 Copilot exposed security risks the organization already had; they did not have the right access controls in place to protect their sensitive information. If they had not paused their pilot to address these risks, their sensitive information could have been exposed.
The lesson here is clear: before deploying Microsoft 365 Copilot, it’s essential to ensure your data is ready. Take stock of your data and verify that it’s well-organized, well-governed, and well-protected. This means setting up proper access controls, classifications, and permissions to ensure that only authorized personnel can access sensitive information.
Remember, Microsoft 365 Copilot is a powerful solution that can and will pull information from anywhere it has access. This is what makes it so valuable; you don’t need to sift through hundreds of documents to get the information you need. However, it respects your privacy and security settings, so it will only access the data that you have permission to access.
Protect Your Data with Visibility Into Access Controls
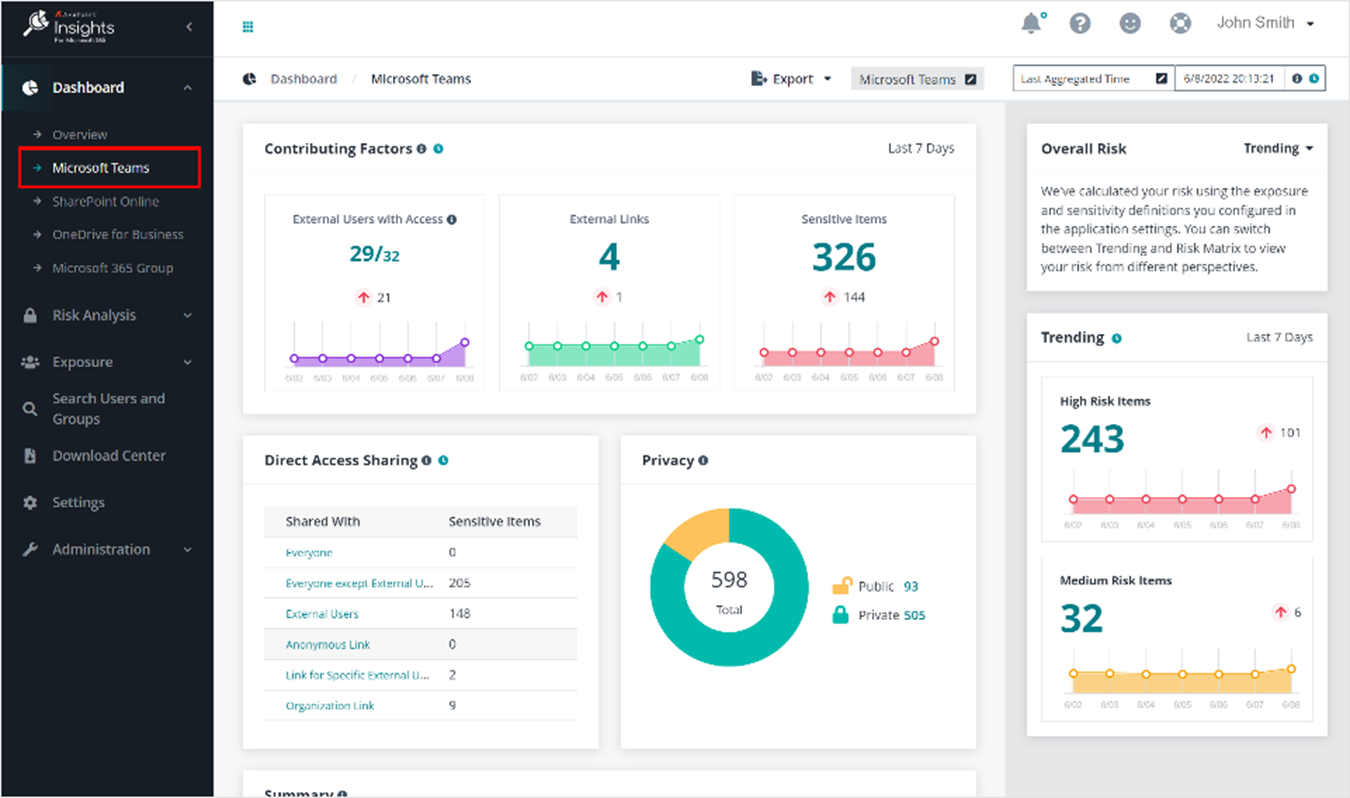
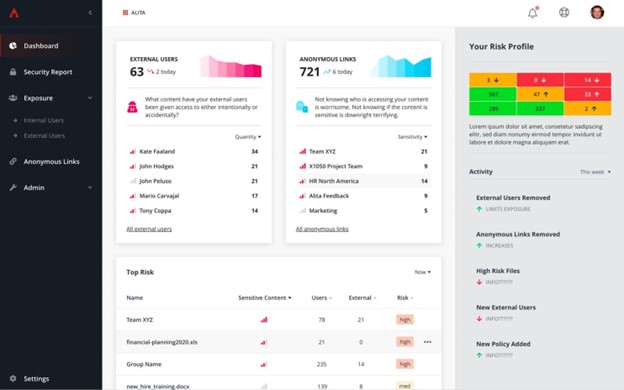
Once AvePoint’s partner realized they couldn’t move forward with their pilot without fixing the data exposure issues, they turned to AvePoint to see if they had a solution that would give them visibility into the state of their access controls. AvePoint Insights addressed the issue perfectly.
With object- or user-based security searches, AvePoint Insights provides unmatched insight into SharePoint, OneDrive, Groups, and Teams permissions, allowing organizations to easily identify potential data risks and address them before deploying Microsoft 365 Copilot.
AvePoint Insights offers highly actionable reporting based on Microsoft’s sensitive information types and exposure. This allows you to audit your sensitivity labels and identify any risks based on factors like sharing permissions and classification without having to look across each individual workspace or security group.
By diving deep into permissions and exposures across your Microsoft 365 tenant, AvePoint Insights helps you determine if permissions for a site containing sensitive information are still effective or if they need to be altered. If the solution flags an issue, you can adjust your security measures from within the tool in response to what it finds.
For example, you may have categorized a workspace as “General,” but Personally Identifiable Information (PII) or other sensitive information is stored there. Insights will flag this oversight, allowing you to change the classification to content categorization “Confidential” and update the tags on the workspace and its content to ensure access to this sensitive data is limited.
Thanks to AvePoint Insights, our partner identified actionable changes needed before restarting their Microsoft 365 Copilot implementation. Once these issues are resolved, the pilot will be up and running again – likely in a matter of weeks.
By using AvePoint Insights to identify and address potential data risks before deploying Copilot, organizations can take a proactive approach to data security, avoiding potential data breaches and other security issues while using the AI solution and ensuring their data remains secure over time.
Looking for more information on how to work effectively and efficiently with Microsoft 365 Copilot? Join AvePoint and Microsoft for our free webinar.
3 Steps to Ensure Microsoft 365 Copilot Data Readiness
As you begin to dive into Microsoft 365 Copilot, ensure the security of your data by taking these three steps:
- Identify: Begin by scanning your environment for any security risks, such as unprotected PII or financial data. You can do this manually by reviewing each workspace’s content and corresponding site permissions, or automatically with AvePoint Insights. Remember, if you skip this step, Microsoft 365 Copilot users could eventually find these vulnerabilities – so take the time to identify them before an exposure occurs.
- Secure: With a good sense of the common security risks in your environment, you can train users on the proper controls they should implement to keep it secure. Alternatively, leave no room for error and use AvePoint Policies to automatically apply the necessary security rules to your Teams, Groups, Sites, and OneDrives, or your entire Microsoft 365 tenant if needed. AvePoint Policies proactively monitors configuration drift, notifying and reverting out-of-policy changes as often as every two hours. This ensures proper access controls and permissions are applied without relying on end-user execution.
- Monitor: Once your environment is in good shape, you’ll want to keep it that way. Regularly monitor permissions and access controls to ensure they remain up-to-date. AvePoint Insights offers automated reporting for IT in at-a-glance dashboards, as well as proactive alerts to flag anything amiss. You can take this a step further by requiring workspace owners to regularly recertify the membership and permissions of their workspaces (AvePoint MyHub makes this easy…and automated).
By implementing reporting and renewals on permissions and access controls, you can stay on top of potential data risks and ensure that your data remains secure even as you use AI like Microsoft 365 Copilot.
READ MORE: What is Data Security - The Complete Guide
Get Started: Prepare Your Data for Microsoft 365 Copilot
Microsoft 365 Copilot has the potential to redefine how you work, but you need a proper foundation in place to ensure your data stays secure. While using AvePoint Insights to scan your environment for potential risks is a critical first step to prepare for Microsoft 365 Copilot and other AI applications, you must have quality data and a robust data strategy to ensure your organization’s privacy and security to fully harness AI’s full potential.
Take the first step to enable Microsoft 365 Copilot data readiness with AvePoint. Learn more about our approach to AI by visiting our website and registering for our upcoming webinar on Microsoft Copilot.