Planning to make the move to Office 365 this year? Get expert advice during our upcoming webinar “Out Hustle The Hassle: Office 365 Migration Planning and Preparing!“
Hi everyone! Today we’re doing a deep dive into understanding Office 365 Groups technical limitations and boundaries, and giving you a few tips to help you overcome!
Office 365 Groups and IT Governance
Microsoft defined a new collaboration milestone with Office 365 Groups – it’s the glue that connects all your Office 365 services. When you enable Office 365 Groups, companies and their employees collaborate more efficiently by integrating multiple services in one user interface. In the near future, almost everything should become a Group and will use SharePoint as central data repository. Microsoft made it easy to create new Groups almost everywhere in Office 365, making it super easy for employees to create and experiment with these Groups.
To learn about customizing and automating SharePoint workflows sign up for our webinar on creating and migrating Nintex workflows. Register now >
But what does all of this mean for governance across all of those services? Native Groups settings help you enforce certain policies, for example protecting your Group’s content against unauthorized access. However, the default settings are not enough to ensure comprehensive governance controls.
When using the default settings, there is bound to be chaos, and IT will lose the control over shared data. In order to avoid this, I want to make you aware of the default settings and their limitations, which must be supplemented to achieve strong Office 365 Groups governance.
1. Understanding Office 365 Groups Limits
By default, every single user is able to create up to 250 Groups. This limit, however, does not apply to Office 365 administrators. The entire tenant can host up to 500,000 groups total. This may sound like a huge number, but is easy to reach when employees are experimenting with Groups – simply creating a new plan in Microsoft Planner creates a new Office 365 Group.
We recently saw this right here at AvePoint. A regional sales team accidentally created two Groups for the same exact purpose and had to delete one – but they deleted the wrong one. Once you delete a Group, it’s gone forever. However, soft delete is on Microsoft’s roadmap.
2. Understanding Public or Private Groups
While creating a new Office 365 Group, the requester has the choice to declare the Group as public or private. The default value is public, which means that all tenant users are automatically granted permission to it. You can easily change this value to private, but think about how often employees will forget that.
Microsoft states the data is safe and nobody will be able to access it if he or she does not have permission to do so. Basically, that’s correct, but this concept is based on SharePoint permissions. If every tenant user gets access to each public Group by default, they can also view and open all the data in those Groups.
A little secret exists behind the scenes and is accessible via PowerShell when it comes to Office 365 Groups permissions. You can use the HiddenFromAddressListsEnabled cmdlet and set it to ”True“. This will hide the Group from the organization’s public directory, giving you one more layer of security and control for the most sensitive Groups.
3. Understanding Office 365 Groups Permissions
Keep in mind that all tenant users will get access to each new public Office 365 Group. Even worse, they will also have edit rights to the entire Group site collection and will be able to change and update documents. Members of the owner‘s Group will even become site collection administrators. This means they will get access to all the special features like Audit Logs, Site Collection Features or they can even delete this site collection. Is this intended? In SharePoint directly, we are also very concerned about these high privilege roles.
With most controls left to your end users, how can IT manage Office 365 Groups? We have another excellent blog that helps answer this question in depth by providing Office 365 Group administration methods that are available natively in Office 365.
4. Understanding Groups Sharing Permissions
Even if an Office 365 Group is not public, members will have the capability to share this Group with anybody – even with external people, if configured in the tenant. So, what happens to the sensitive data, which the company probably wants to share within Groups?
5. Understanding Office 365 Groups External Users & Collaboration
Another default Office 365 Groups setting is the ability to share a Group with external people who are already listed in the corporate directory. That means external people with an Office 365 account from this tenant will be considered as internal, and therefore will be able to further share permissions with anybody, even if sharing with “real” external users is prohibited.
6. Understanding Groups Storage
Office 365 Groups Site Collection will not appear in the central SharePoint Online administration, which his significant because they cannot be managed from there via the user interface. And by default, there is no storage limit for Office 365 Groups. Thus, you can easily reach the SharePoint storage limit.
Go beyond default settings when managing your Office 365 groups! Check more about how you can overcome these limitations through AvePoint’s Office 365 Governance solution!
Implications of Office 365 Groups Technical Limits and Boundaries
When we now rethink all these default values, we realize the following problems:
- Group sprawl
- No access control to the Groups content for internal and external colleagues
- Rapid data growth without limitation
With this in mind, it’s best to configure governance policies in order to get back control over Office 365 Groups for tenant administrators. You cannot cover every governance wish you have, but at least you should use the available capabilities.
Ok, what can we do?
- If you need more than 500,000 Groups, you can give Microsoft a call and ask for a higher limit.
- If you want to set the default Groups category to ”Private“ or eliminate the “Public” option entirely, you have no choice.
Nevermind! Fortunately, we can configure settings #3 through #6 and therefore address the three mentioned problems.
1. Overcoming Group Sprawl
Limit the group of colleagues who can create Office 365 Groups:
A highly recommended approach to overcome this problem is the limitation of permission so that not every user is able to create Groups. This can be achieved by changing the Office 365 Groups template and creating a dedicated security group, which covers all eligible Group creators. This is only possible via PowerShell and will be explained in high detail in a later technical post.
Question:
If I allow the creation of Office 365 Groups only for a certain security group, do I also need to add the administrators to this group to let them create Office 365 Groups?
Answer:
Yes and no. It depends on what you consider an “administrator.” Furthermore, some built-in administrators will be eligible to create Groups, some others will not. The following list of administrators will be able to create Office 365 Groups, independently of being member of the mentioned dedicated security group or if Groups are deactivated entirely:
- Global Administrators
- User Management Administrators
- Mailbox Administrator
- Partner Tier1 Support
- Partner Tier2 Support
- Directory Writers
Best Practice:
Let only a few people create Office 365 Groups or disable creation entirely. The above mentioned administrators will still be able to create Groups via the Office 365 Admin Center or via SharePoint (only).
Group Classification:
In order to establish a better overview of all existing Office 365 Groups, you can classify them with metadata. In this case, you can configure via PowerShell (only) a list of keywords, from which a Groups creator can choose while building a new Group. The key word will become a property of this Group. This is similar to the already known property bag values for a site collection.
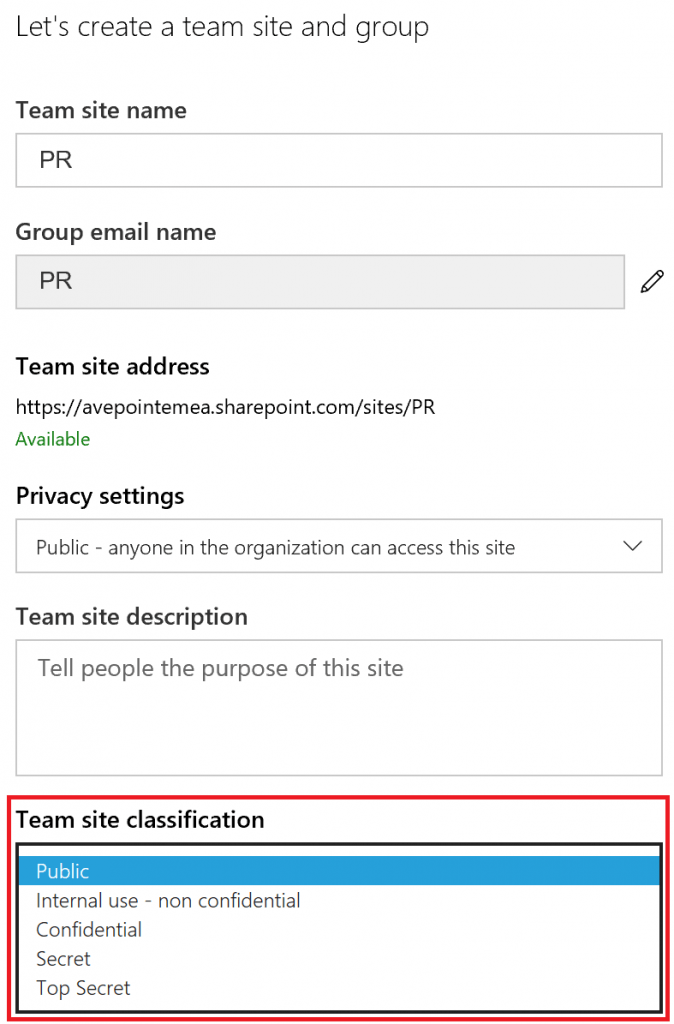
The Good: I can add or change the Groups classification for existing Groups.
The Bad: This is the one and only metadata tag we can add.
The Ugly: The selection of configured keywords for a new Group is only available in the SharePoint user interface, but not in any other Group creation entry point.
Best Practice: Try to add keywords to your Office 365 Groups in order to structure them. To achieve this, use SharePoint only for Groups creation or PowerShell after creation. Third-party tools can also help.
Groups Naming Policies:
In addition to the classification capabilities, we can also define prefixes and suffixes for Office 365 Group names in order to classify them. More than one prefix or suffix is possible. One prefix or suffix can be just text, or you can also let Office 365 read out account attributes from the user, who creates the Group. This is the <Department> in the screenshot below as an example.
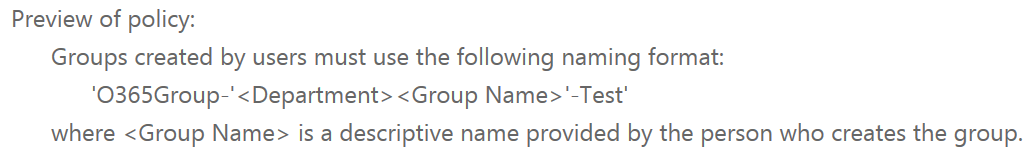
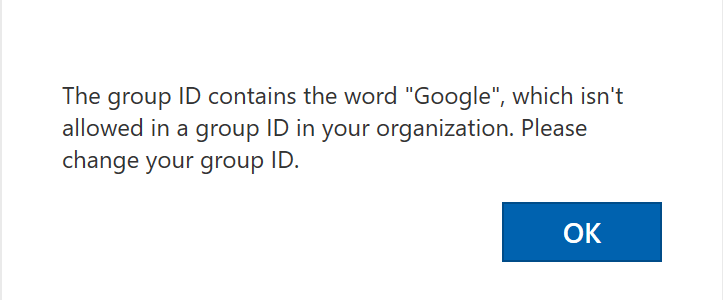
You can also define a “blacklist” of words or characters that are permitted for Group names. If such a word is used for a new Group, the user will get a corresponding dialogue box.
Be careful: Naming policies will only apply when creating a new Office 365 Groups via the Office 365 Admin Center and in the Mail or People view, but not in SharePoint and Planner.
Best Practice: Use naming policies for your Office 365 Groups in order to separate them from standard SharePoint sites or email groups and reserve certain names, which are planned to be used for other purposes.
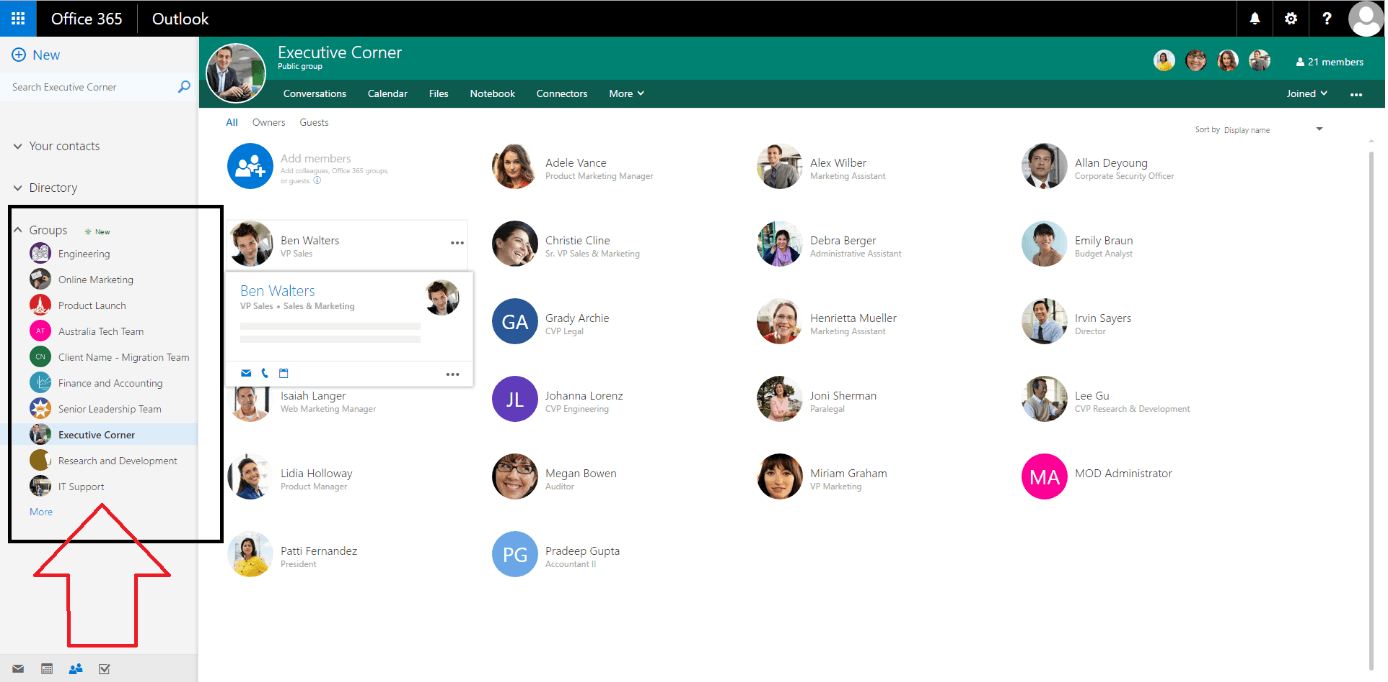
Monitoring Group Sprawl:
For the easiest overview of all your Office 365 Groups, I recommend the central group view in Office 365 Admin Center. We can manage and delete all groups from there. Furthermore, this approach is recommended, because:
- The Groups site collections are not visible in the SharePoint Administration Site
- In Exchange administration, Groups created within Planner or SharePoint are not visible
- The ”Discover” view in SharePoint is not very user-friendly with many Groups
PowerShell is also always an option, but not as easy to use as the central Group view in the Office 365 Admin Center.
2. Overcoming Groups Access Control Limitations for Internal and External Users.
Restrict Permissions:
For permissions and sharing with internal and external colleagues, there are also a couple of PowerShell configurations and workarounds available in SharePoint. For the Office 365 Groups template, we can configure the following three properties:
- AllowGuestsToBeOwner
- AllowGuestsToAccessGroups
- AllowToAddGuests
If these options are disabled – or at least partly disabled – the security of all newly created Office 365 Groups will be much stronger. However, we cannot manage granular permissions – with a new Group, there will only be visitors, members and owners.
Additionally, we can define URLs, which lead to webpages, where you can share usage guidelines for internal and external colleagues. This will drive user awareness about shared Groups content, which could be sensitive.
- GuestUsageGuidelinesUrl
- UsageGuidelinesUrl
For existing Office 365 Groups and share permissions, I can only recommend the manual workaround: Manage the member’s permissions in the Group’s Site Collection or use PowerShell.
Best Practices: Limit the permissions of Group members with the available template options. Address individual requirements after a Group’s creation via Office 365 Groups PowerShell or use third-party tools to manage granular permissions proactively.
3. Overcoming Rapid Data Growth without Limitation in Groups
Limit the Group’s Storage:
The third problem is manageable via SharePoint Online PowerShell cmdlets. We can consider the Group site collections as standard site collections and add a storage quota. The requirement for manual quotas is also manual storage management, which you can configure in SharePoint Online settings. Although this is a good and easy approach to limit the storage growth, it’s still only a workaround, because we cannot configure Group quotas proactively with native capabilities.
Best Practice: Monitor the data growth for your SharePoint and Groups storage.
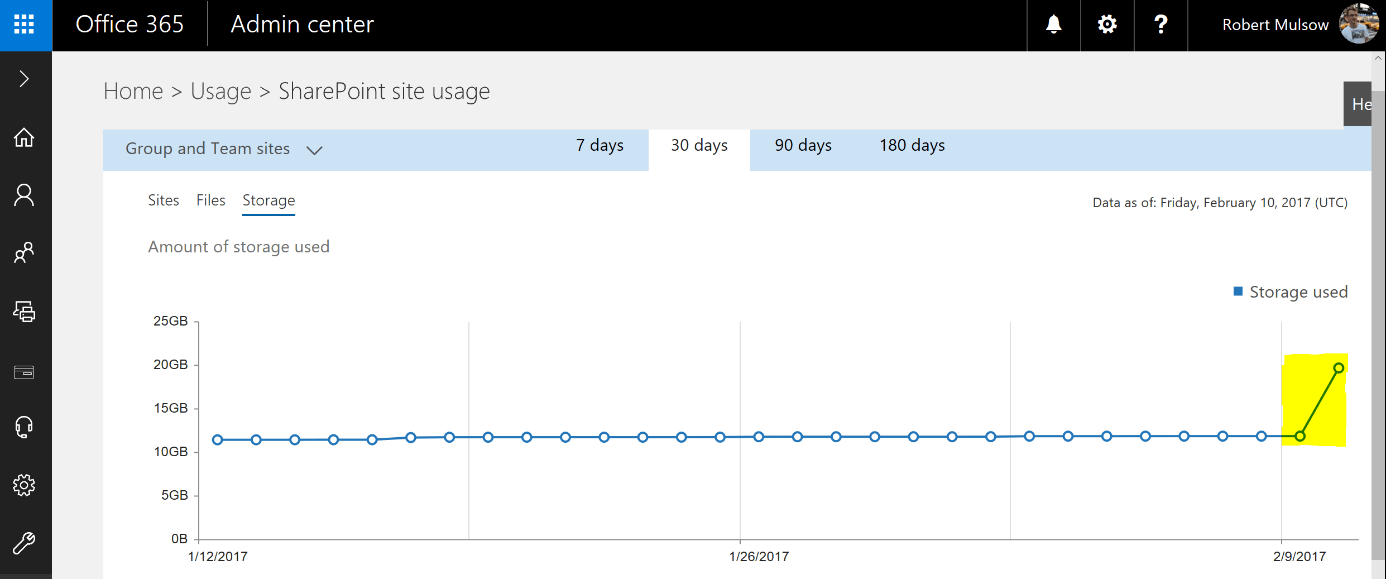
If storage is growing rapidly, I recommend configuring manual SharePoint storage management and apply quotas for your Groups afterwards.
Summary: The default Office 365 Group settings are not enough for solid data governance. However, Microsoft already delivers a couple of options, which just require your configuration in order to increase security and structure. Nevertheless, these options cannot satisfy complex governance requirements, and we also identified inconsistencies in regards to classification or naming policies.
No need to worry though, because Microsoft is continuously improving the Office 365 features and even share its Office 365 Groups roadmap with us. Have a look into this or seek third-party tools to eliminate any security concerns and start utilizing the great advantages of Office 365 Groups.
Happy “SharePointing“!
More From The Office 365 Groups Playbook
If you’re interested and looking for more information about the purpose of Groups and why you should care, check out this great video post by Dux Raymond Sy, where he interviews Microsoft’s Program Manager for Groups, Christophe Fiessinger.
Blogs about Groups | On Demand Videos |