Learn “When to Use and How to Manage Microsoft Teams & Office 365 Groups” in our downloadable ebook!
Office 365 adoption is on the rise in both the commercial and public sectors. However, with growth also comes concerns; how can you best govern this expansive beast of a software collection?
Office 365 offers a plethora of services: Outlook, SharePoint, Planner, Groups, Teams, Yammer, etc., and managing all of these can be daunting for administrators who are used to having full control of their platforms. This becomes even more intimidating for tenant owners who provide Office 365 as a service for others to consume, each with their own wants and needs.
As large, disparate, organizations and agencies look to cut costs, consolidation of services becomes a primary focus. Office 365 tends to be one of the services that can be a shared offering among departments and divisions. However, while it is an effective cost-saving decision, it can become problematic for those who are used to operating on their own and having total control of their environment.

When operating under a shared tenant model, it is impossible to separate administrative privileges in a way where Admin A can only see his department’s content and no one else’s. A SharePoint administrator (not to be confused with a site collection administrator) can see all of the SharePoint site collections in a tenant. Likewise, an Exchange admin can see all of the mailboxes in a tenant. This results in one of two options:
- Give every department administrator elevated admin rights and access to all of the content surrounding the service they oversee.
- Give no administrator has elevated rights and leave it up to the service provider to keep everything in check.
These two options also lead to one of two issues:
- Other departments might go up in arms because there are additional administrators with elevated permissions to their content (which may be deemed private or sensitive).
- Administrators could petition for additional privileges because their department has special considerations surrounding governance.
However, this mindset is usually derived from past habits. The key to changing it is understanding that global administrators should define the governance policies in a shared tenant because it’s common for multiple departments to share the same concerns. Instead of attempting to set the same policy multiple times, tenant owners can set a baseline that will apply to all and account for unique needs as necessary. This is what I call a top-down governance approach.
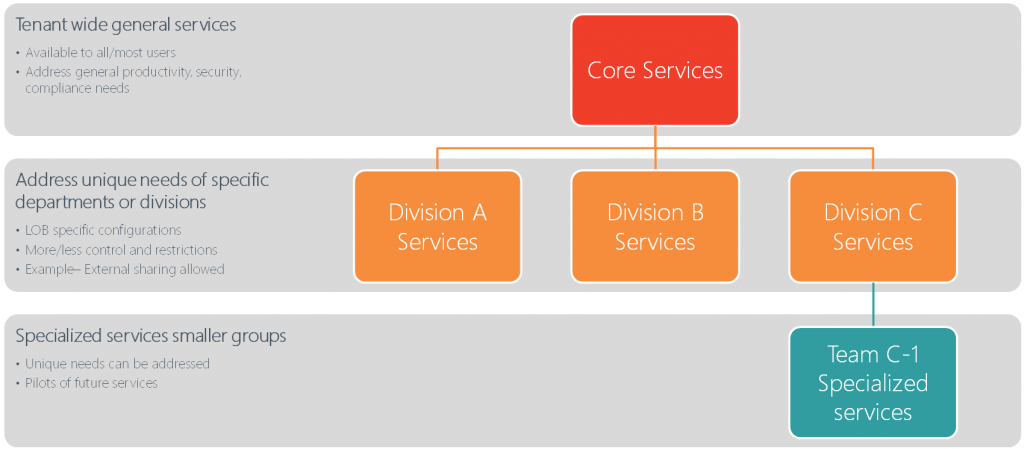
The above diagram breaks down this concept and highlights how this approach is implemented:
Tenant Level
At the tenant level, there will be governance policies put into place that address the generic needs that are shared by all departments. These policies are usually around security and compliance concerns.
Department Level
Business-specific needs can be addressed at the department level. These policies will have more of an effect on the department itself and how workers collaborate, conduct business, etc. These governance controls will come in the flavor of external sharing controls, permission configurations, metadata concerns, etc.
Industry Survey: Office 365 Governance and Migration
Ad-Hoc
Specialized or otherwise unique needs can be handled ad-hoc. In the event that there are needs that are unique to a particular group of individuals, changes can be handled on a case-by-case basis. This should not be the norm, but there should be a plan in place to handle these concerns.
In the event that you’re unsure how something like this can be set up in your environment, check out AvePoint’s governance solutions. These solutions have the ability to implement the delegated structure seen above and automatically enforce the policies that are put in place.
Data governance doesn’t have to be difficult! It just takes the right team, framework, tools and a little bit of patience to get it right.






